Regulus Cyber, an Israeli firm that provides a solution for smart-sensor security, has introduced a breakthrough software-only cybersecurity solution designed to protect global navigation satellite system users (GNSS, also known as GPS) from spoofing attacks.
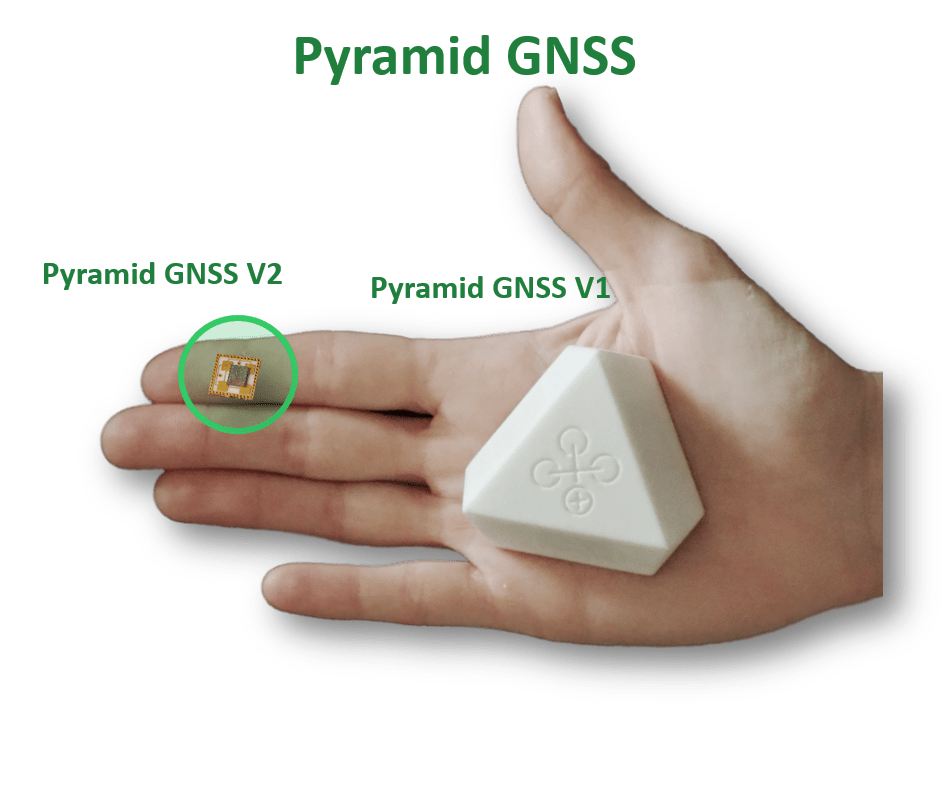
The new Regulus Pyramid GNSS is a stand-alone software solution that doesn’t require any additional hardware to protect a GPS receiver or chipsets—ensuring the security and reliability that are essential to safe and accurate navigation across a wide range of applications including automotive, mobile, aviation, maritime and critical infrastructure.
GPS spoofing is a remote attack that transmits fake PNT (Position, Navigation, Time) information, enabling a hacker to take control of a target using satellite navigation and affect critical functions, such as time-sync, speed control, steering, navigation, location, privacy and more.
GPS spoofing attacks are notoriously difficult to detect and guard against, and becoming increasingly frequent as hackers use spoofing for personal monetary gain and various other intentions. The Regulus Pyramid GNSS™ solution uses proprietary algorithms to accurately determine when spoofing occurs and provide real-time protection at the receiver level, according to the company.
“We’ve learned how to perceive anomalies between legitimate GNSS signals and spoofed signals by researching the variations in the satellite signals protocol, and recognizing the inter-relationships between signal parameters,” Regulus Cyber CTO and co-founder Yoav Zangvil explained. “Now we can offer our customers the extremely important assurance that they’re receiving legitimate signals from satellites, and not unsafe false signals coming from ill-intentioned hackers.”
Regulus Pyramid GNSS supplements GPS receivers, including legacy receivers and Android operating systems, offering dependable protection. In addition, online services from Regulus Cyber can provide further signal authentication to connected fleet operators in real-time.
The effects of GNSS spoofing are problematic—and often potentially dangerous—across multiple industries:
- In automotive applications, spoofing can cause cars to drastically speed up or slow down, and can cause aggressive braking, steering, and accelerating, exiting at the wrong interchange, or reporting an incorrect position to 911 in emergencies
▪ With cellular devices, spoofing renders location-based services (LBS) such as Google Maps, Waze, and Uber unusable, and make users appear to be in particular locations when in fact they’re elsewhere, with major privacy implications
- With infrastructure, spoofing results in reports of the wrong time, causing other system-dependent errors, such as railroad services delays, electric power grid blackouts, and financial systems failures.
- Global shipping and aviation heavily depend on satellite navigation, and spoofing attacks result in major and long delays.
“As proven in our recently published experiment with a Tesla semi-autonomous vehicle, the spoofing attack resulted in taking control of the target’s autopilot navigation and being able to redirect the vehicle to a different route,” Regulus Cyber CEO and co-founder Yonatan Zur said. He added that, according to a recent study by the European Satellite Agency, there will be over 8 billion GNSS receivers used worldwide and that means every system is potentially hackable by spoofing, and “As the dependency on GPS grows so does the vulnerability of our modern transportation systems, especially as we head towards an autonomous technology future.”