Improvements to GPS performance are often incremental, achieved by squeezing better performance out of existing systems with clever tweaks, smarter analysis and sharper receivers. Then again, every once in a while, there’s a huge leap in the capabilities of the system itself—an advance so big that it makes you appreciate all over again the elegant wizardry of satellite navigation.
Federal researchers are set to test just such an advance, an enhancement to the GPS L1C signal that should make it easy for an enabled receiver to tell if it is being spoofed.
“You’ve heard the challenge of being able to download GPS spoofer software from GitHub and loading it on a HackRF software-defined radio—therefore anyone can really spoof if they’ve got $1,000. Well what they’re doing here is going to make it extremely difficult for someone to do that,” said Kevin Coggins, who focuses on making Positioning, Navigation, and Timing (PNT) more resilient as the vice president leading Booz Allen Hamilton’s PNT service offering.
The new technique adds encrypted watermarks to the L1C signal that not only let users know when a signal is being spoofed but also makes it possible to authenticate the location of a GPS receiver to another party. This later capability could enable firms to more easily thwart would-be hackers by blocking those unable to prove they are sending from expected and/or appropriate locations.
“The current state of affairs in anti-spoofing receiver design reveals numerous vulnerabilities,” Logan Scott wrote in a 2003 paper introducing the technology. “Some of the spoofing detection measures in wide use offer a false sense of security. Authenticatable signal architectures are needed.”
Chimera
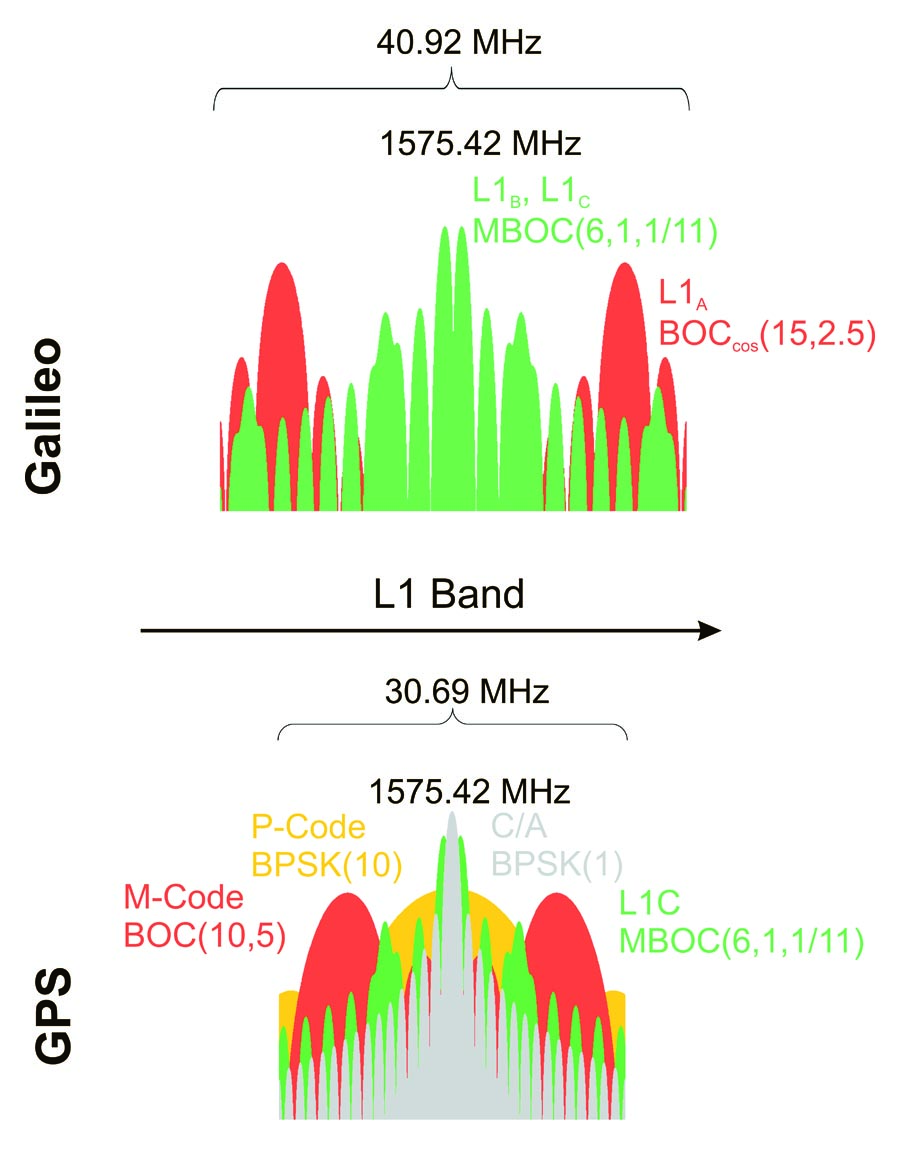
The technology Scott proposed is Chimera or Chips Message Robust Authentication, which is now being tested on L1C by the Air Force Research Laboratory. AFRL is adding the experimental signal to the NTS-3 satellite (Navigation Technology Satellite 3), which is set to launch in 2022. The work is being led by AFRL’s Advanced GPS Technologies program, which is part of the Space Vehicles Directorate. In April AFRL released Interface Specification IS-AGT-100, a new Space Segment/User Segment Interface for the experimental signal and is seeking feedback from the satellite navigation community (see box).
Chimera involves encrypted, steganographic watermarks that are encoded into the signal by the satellite. The signal is recorded by a receiver and then decoded with a key that is sent after a slight delay. Once a key is sent the system changes the key. Since the signal is already in the user’s receiver before the key is sent, a spoofer will not have the correct key ahead of the real signal going out. This makes spoofed signals easily detectable. Either they won’t have the watermarks or the watermarks and key won’t match up.
“Basically what we’re doing is we are coding this into the signal. You can’t see it in real time but you can go back and look at it and establish that that really did come from a satellite,” Scott told Inside GNSS. The approach is specifically designed for civil users and does not require them to hold onto keys securely. “As soon as the keys are published they are no longer suitable for real time watermark generation,” he said.
The keys can be delivered via the GPS signal itself, which involves a 3-minute delay, or through other faster channels like an augmentation system (6 seconds) or an internet connection (1.5 seconds).
The 3-minute channel latency for signal-based delivery is driven by the data rate available on the GPS signal, explained Joanna Hinks, the principal investigator for the AFRL signals research team. “We need to have enough time to deliver the entire digital signature and still get the rest of the necessary ephemeris data down to the user. So that was our assessment of how long it would take us to reasonably deliver the signature and not use the entire data channel to do it.”
The 6-second key delivery time is based on the assumption that the key would be delivered over the air from, for example, a geostationary augmentation satellite. The short one-and-a-half-second delivery time assumes constant access to a secure, higher rate communications channel on the ground. “We specifically chose 1.5 seconds because it aligns with the Z count,” said Hinks. (GPS tracks how many seconds since the beginning of the week, doing it in 1.5-second intervals that comprise the Z count.)
“We also didn’t want to go much faster than that because the security against attacks depends on having user time accurate to at least as good as that latency,” said Hinks. “So if you’re going to have a 1.5 seconds latency, your user time needs to be good to within about a second in order to guarantee that no one’s using a replay attack against you.”
There is another reason that the quickest key transmission time is 1.5 seconds—even low-cost receivers are accurate to about 1 second.
“Maintaining one second accuracy for some reasonable amount of time is generally not too challenging of a problem,” said David Chapman, the program manager for AFRL’s Advanced GPS Technologies program.
AFRL has taken some pains to help Chimera slip into the current GNSS ecosystem as seamlessly and quickly as possible.
“One of the reasons that we chose L1C as the first signal to try and implement this Chimera algorithm was partly because of that commercial nature. And knowing that they (industry) can probably move a little bit faster than DOD (the Department of Defense) in order to implement some of these things,” Chapman told Inside GNSS.
That choice was bolstered, said Hinks, by the fact that L1C is not being broadcast operationally yet. “They’re just testing it right now on the first GPS III satellite. So presumably there are fewer manufacturers who already have a mature receiver design for that.”
Chapman said AFRL has also been talking with Lockheed Martin, the prime contractor for the GPS III and GPS IIIF satellites, to see if a Chimera-enhanced L1C signal could be implemented on at least some of the GPS III satellites and become part of the baseline for the IIIF spacecraft when they start launching. “We’re pretty sure there’s not a hardware change needed to do this,” Chapman said.
There is another near-term possibility too—to add the signal enhancement to the Wide Area Augmentation System (WAAS). This approach would be faster because the WAAS signal is generated on the ground and then broadcast through a satellite. Tweaking on-orbit hardware is unnecessary.
The approach to using WAAS would be similar but not quite the same as having it on GPS L1C. Receivers would use WAAS as an authenticated measure of what the signals should look like.
“Some of the space-based augmentation systems, the satellites, are capable of providing a ranging signal and not just a differential correction,” explained Hinks, “and if you can put this on any ranging signal then you can use something similar to the Receiver Autonomous Integrity Monitoring—RAIM, that they already used for aircraft—and basically do a consistency check.”
To do this you compare all the non-enhanced signals to the signal authenticated via Chimera. If you find an inconsistency, it might indicate that some of your non-protected signals are being spoofed and should be disregarded.
Scott said that, in his personal opinion, should the government decide to add Chimera to WAAS, the new capability could be up and running in about two years.
But would the government be interested? Coggins believes the military would be. Definitely.
Defense Applications
“Decision makers across the Department of Defense—they’re looking how to make sure their systems are resilient against these threats. When they want their systems to provide PNT, and then work seamlessly in a threat environment—those are the decision makers that are going to say: ‘Hey, what is this? This looks like a smart thing,’ “Coggins said. And he should know. Coggins was a direct-reporting program manager for Position Navigation and Timing (PNT) within the Army Acquisition Corps. He was also their assured PNT cross-functional team director.
“What David Chapman and the AFRL team have done here. They’ve taken some known issues in signals we’ve used for a long time and they’ve come up with really innovative ways to address those issues. So what they’re doing here, what this interface spec does, is it increases the resilience and reliability and operational readiness of the systems that depend on PNT through some very smart things in the signal. So, that said—putting my program manager hat on and my CFT director hat on that I used to wear—I would absolutely be moving toward adopting L1C.”
Coggins noted that almost every system that uses the protected SASSM architecture (Selective Availability Anti-spoofing Module) and the P(Y) code signals—that is the military signal—have to get time initially from L1 and specifically from the C/A code, the commercial signal. “So they all have a dependence on that unprotected commercial signal. I’d rather them have a dependence on L1C in order to get time so they can move towards the military signal.”
Location, Location, Location
The attraction for commercial users, may be even greater given that Chimera also enables users to verify their location to other parties. The idea is that the user’s GPS receiver would record the whole signal, that is the watermarks and the signals themselves, and then send all that data to the person needing location verification before the keys change. That second party then uses the keys to check the watermarks. As each combination of watermarks and signals is unique to the place where it was recorded it would be very difficult for bad actors to fake the data package and thereby their location.
The data packages for doing this sort of verification are small, 150 kilobytes, said Scott—about the size of a small jpeg image. “So (I) record the signal I then send it to you before the keys have been published. Now you’ve got a copy…I could have forged the signal but I’ve no way to forge the watermarks. You’re sitting there holding this and then the keys are published and then you can look at this and you can establish two things. One, you can establish a position where that recording was made and two, you can establish when watermarks are present as expected. And if they are not, then you have an indication that this is a forged location.”
That authenticated location will also be pretty accurate, said Scott. “Basically I could tell if the signal was recorded at your house or your next door neighbor’s house because embedded in this information—the raw recording—is, in a sense, the whole GPS signal constellation.”
This secondary Chimera capability could help keep hackers out of SCADA systems (Supervisory Control And Data Acquisition systems)—that is the hardware and software that controls industrial operations and a lot of critical infrastructure.
“In the Ukraine they are having all kinds of problems with their power plants,” said Scott. “…Specifically what’s happening is that the SCADA systems are being hacked into and then people are throwing in bad commands that make power plants go bad—they get sick. And so if you know where the commands were coming from that would give you an additional measure of security there. Now it’s not 100 percent, but it definitely adds to the complexity for an attacker because now he has to somehow convince you the commands are coming from a particular location.”
New Receivers Necessary
The anti-spoofing and anti-hacking advantages to the commercial sector are such that Chimera advocates are hoping companies will develop new receivers, which will be necessary, Scott and Hinks agreed.
“You need to have the capability of storing some data and (doing) some post processing,” said Hinks. “…The digital signature information that tells you where to look for the watermarks—the markers—that depends on something called bit commitment, which means that the information about where to look arrives after the markers are sent. So in order to maintain that bit commitment aspect, where the information comes after the transmission, you need to be able to store the signal for at least a few seconds so that you can look back after the fact.”
“As far as I know there are no COTS (commercial off-the-shelf) receivers that are currently designed to operate in that way,” said Hinks, “but it’s not a major architecture change to add some memory.” She added that firms could use commercial memory chips to add such capability.
Coggins is hoping the private sector picks up on developing Chimera receivers because it will bring costs down for defense users. “In fact if commercial industry adopts this signal, that means this is going to become very inexpensive to implement for the military.” he said.
Spoofing expert Todd Humphreys, an associate professor of aerospace engineering at the University of Texas at Austin said the “Chimera signal appears to be a solid implementation of Spreading Code Authentication (SCA)” and a technique that has a real chance of being adopted.
“My 2013 analysis of various civil anti-spoofing strategies made it clear that SCA is superior to simpler authentication methods such as Navigation Message Authentication (NMA),” Humphreys told Inside GNSS in an emailed statement. He added, though, that he and others have been worried that the enormous “inertia” of GNSS signal definitions would prevent SCA from ever being implemented in practice, since it cannot be retrofit to existing GNSS signals without altering the signals in a way that violates their interface specification. Happily, he said, Chimera may be able to overcome that hurdle.
“AFRL obviously views the L1C signal structure as not yet set in stone, and to their credit is demonstrating the foresight to introduce SCA. The implementation looks sound to me, and the team that put it together—including Logan Scott and Joanna Hinks—is a trustworthy bunch. Let’s hope that AFRL can move the mountains necessary to get this implemented on L1C!”
AFRL Seeks Feedback on Chimera
The Air Force Research Laboratory (AFRL) is asking for feedback from the Positioning, Navigation, and Timing (PNT) community on Interface Specification IS-AGT-100, a new space segment/user segment Interface for the Chips Message Robust Authentication (Chimera) Enhancement for the L1C Signal. The specification can be found at http://www.gpsexpert.net/chimera-specification and should also be available on the Inside GNSS website. AFRL asks that comments be provided on the form available that the bottom of the page at https://www.gps.gov/technical/icwg/meetings/2019/05/. The button for the form says “Download Form.”
AFRL is in the process of setting up a channel to take comments.
Dee Ann Divis has covered GNSS and the aerospace industry since the early 1990s, writing for Jane’s International Defense Review, the Los Angeles Times, AeroSpace Daily and other publications. She was the science and technology editor at United Press International for five years, leaving for a year to attend the Massachusetts Institute of Technology as a Knight Science Journalism Fellow.