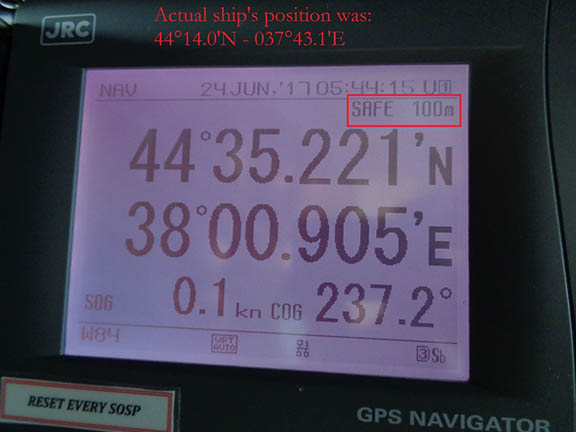
Hackers exposed another vulnerable chink in U.S. national infrastructure over the weekend, in an attack on GPS manufacturer Garmin that began late Thursday, July 23. Although the cybersecurity strike, apparently aimed at extorting a ransom, did not explicitly include the GPS signal, it disabled two large GPS user communities: general aviation (private pilots and some larger commercial flight operators) and fitness enthusiasts. Both found their Garmin devices and apps unresponsive.
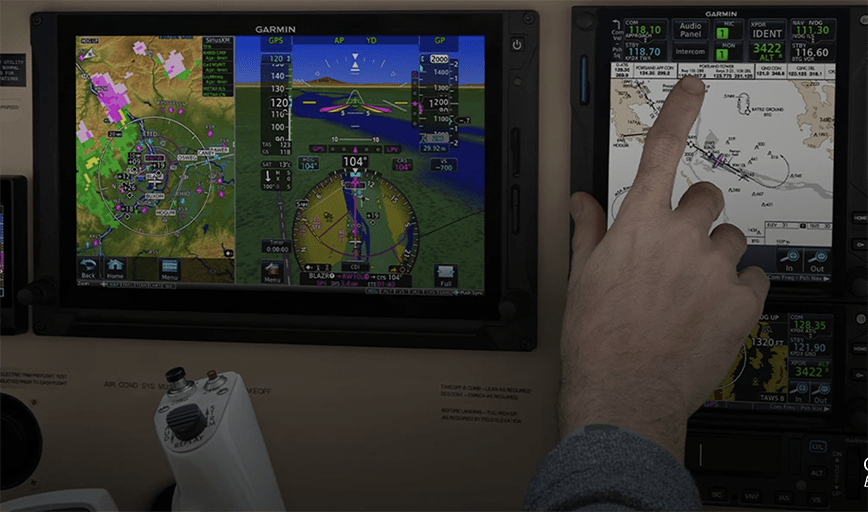
The assault shot down flyGarmin, the company’s primary web service hub supporting data and services for its navigation, communication and data systems provided to thousands of aircraft worldwide.
Garmin stated that it was “the victim of a cyber-attack that encrypted some of our systems. Many of our online services were interrupted including website functions, customer support, customer-facing applications, and company communications. We have no indication that any customer data, including payment information from Garmin Pay, was accessed, lost or stolen.”
It posted a notice to users on its website: ““We are currently experiencing an outage that affects Garmin.com and Garmin Connect. This outage also affects our call centers, and we are currently unable to receive any calls, emails or online chats. We are working to resolve this issue as quickly as possible and apologize for this inconvenience.”
The company quickly undertook a multi-day maintenance shutdown of its website, the Garmin Connect user data-syncing service, its aviation database services, and some production lines in Asia. By Monday morning it was able to announce that “We are happy to report that many of the systems and services affected by the recent outage, including Garmin Connect, are returning to operation. Some features still have temporary limitations while all of the data is being processed. We’d like to thank all of our customers for your patience and understanding. Click for more details.”
During the attack, private pilots were not able to download a version of Garmin’s aviation database on their Garmin airplane navigational systems. An up-to-date version of this database on in-flight navigation devices is an FAA requirement for non-visual flights, that is, either in adverse weather or when needing coordination with the air traffic control system. The Garmin Pilot app, used to schedule and plan flights, was also down, sending those pilots who insisted on flying back to the pencil-and-paper era.
The extent to which commercial and larger aircraft operators’ may also depend on Garmin flight planning services is not known. “General aviation” encompasses everything from small piston aircraft flown by private pilots to large intercontinental corporate jets to emergency evacuation of the sick or wounded (medevac). The class, which is FAA-regulated separately from passenger carriers, includes anything that isn’t airline or military. The latter two classes of planes and pilots typically have satellite-based augmentation equipment (the U.S. Wide Area Augmentation System, WAAS) aboard to improve navigation and reduce risk. It may be that not only private pilots were unable to download databases and access services, but a wider and more economically significant range of operators as well.
Although official details have not emerged, unofficially it appears that the attack came from ransomware, a type of malware that encrypts a database or system, effectively locking it up, and threatens to perpetually block access to it unless a ransom is paid. In a variant, the ransomware may also threaten to publish the victim’s data. The miscreant was possibly one named Wasted Locker, operated by a gang of unknown origin. It has contacted victims after infecting their computers and exacted a funds transfer for files to be returned to their original state.
A $10 million figure has been bruited about in the Garmin case. It is not known whether Garmin paid the ransom; somehow it obtained or derived a decryption key to unlock its digital assets, or it may have restored the data using a backup it had created.
Nor is it known whether Wasted Locker (or other) targeted all Garmin systems or a single one, and the company itself took protective measures. One cybersecurity expert ventured “The fact that other services they offer went offline is no surprise; that is just good protocol. When you don’t know what is happening, isolating systems from further potential contagion or propagation is usually the best course.”
In a further twist to the national knickers, the Garmin outages could have affected military flight operations, as some Air Force pilots rely on Garmin flight instruments and even wrist computers as backups in an emergency. An Inside GNSS story a few months ago detailed how the Air Force purchased some advanced Garmin watches in 2018, and an Air Force general recently stated that his U2 spy pilots employed them to “receive foreign GNSS signals and provide backup navigation when GPS is jammed.”
Government authorities, particularly the Federal Aviation Administration, will doubtless seek details, answers and countermeasures.