September 19, 2017
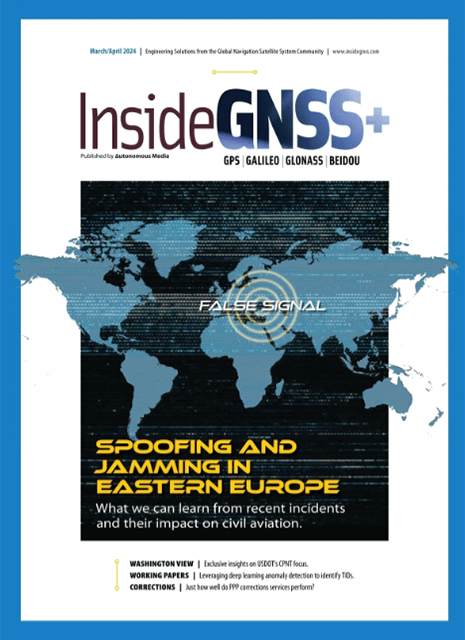
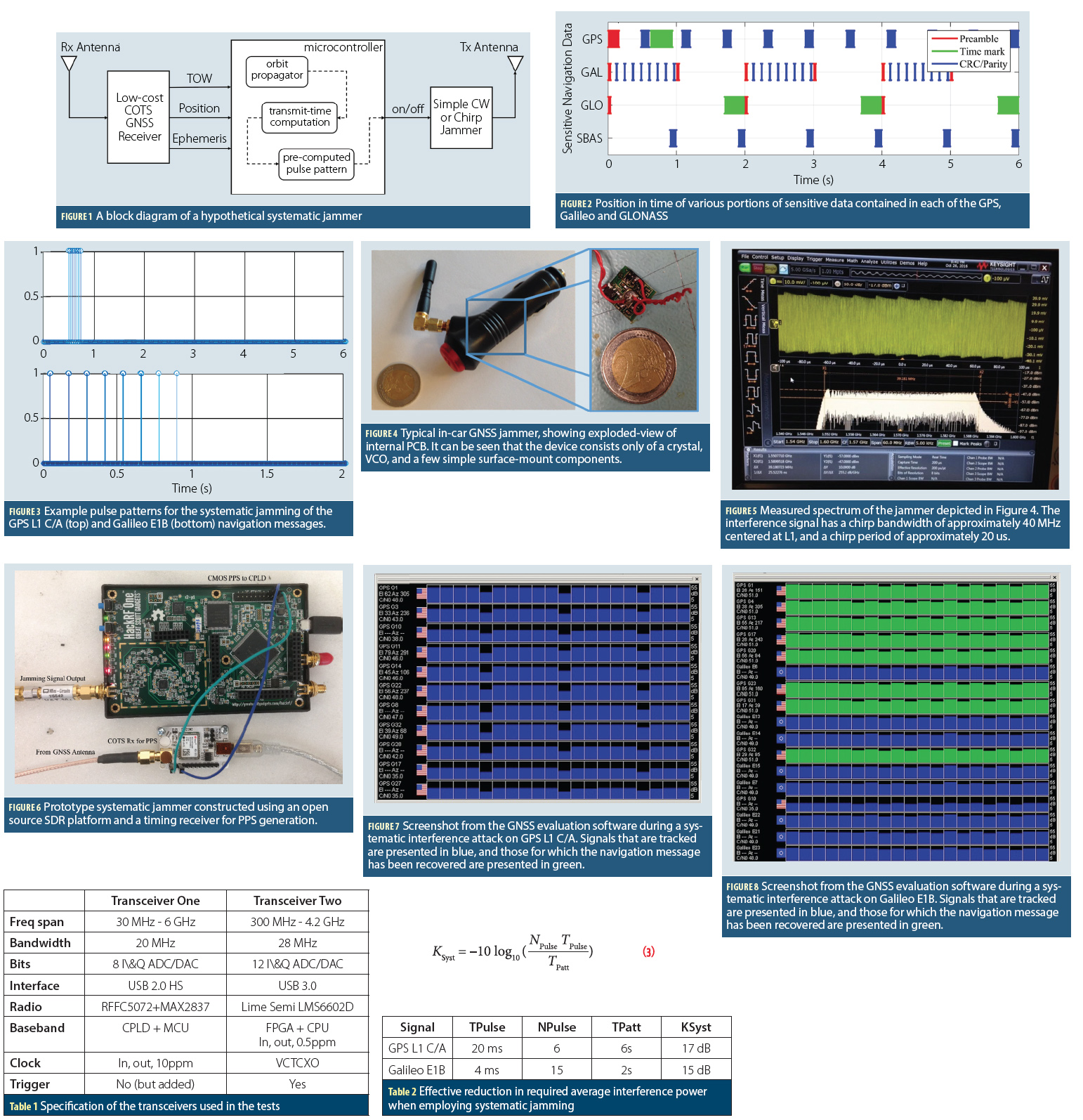 Figures 1 – 8, Tables 1 & 2, Equation 3
Figures 1 – 8, Tables 1 & 2, Equation 3
Systemic Jamming
 Figures 1 – 8, Tables 1 & 2, Equation 3
Figures 1 – 8, Tables 1 & 2, Equation 3The vulnerability of GNSS to various forms of malicious interference have been widely discussed in recent years, and have considered a wide range of both real and potential attacks. Some of these have included extensive studies of commercially available jamming devices, while others have considered the more comprehensive case of spoofing, where the interference takes the form of genuine GNSS signals (For details, see papers listed in Additional Resources, including M. G. Amin et alia).
By Inside GNSS